If you’ve ever wondered how people browse the internet anonymously, you’ve probably heard of Tor. But what exactly is it, and how does it work? Let’s break down this fascinating technology in plain English.
What Is Tor?
Tor stands for “The Onion Router” – and yes, that name is intentional! Just like an onion has multiple layers, Tor wraps your internet traffic in multiple layers of encryption. Originally developed by the U.S. Naval Research Laboratory in the 1990s, Tor has evolved into one of the most important privacy tools available today.
At its core, Tor is free, open-source software that helps you browse the internet anonymously. It routes your connection through a network of volunteer-operated servers around the world, making it extremely difficult for anyone to trace your online activity back to you.
How Does Tor Actually Work?
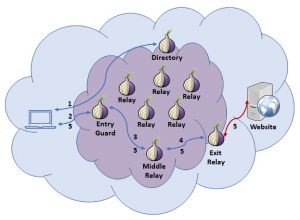
Here’s the simple version: when you use Tor, your internet traffic bounces through at least three random servers (called “nodes” or “relays”) before reaching its destination. Each server only knows about the server immediately before and after it – no single server knows both where your traffic came from and where it’s going.
Think of it like sending a letter through multiple post offices, where each office only sees the address of the next office, not your final destination. This creates a chain of encrypted connections that protects your privacy.
The Three Types of Tor Nodes
Entry Nodes (Guard Nodes): These are the first servers your traffic reaches. They know your real IP address but don’t know what websites you’re visiting.
Middle Nodes: These relay your traffic but don’t know your IP address or your destination. They just pass encrypted data along.
Exit Nodes: These are the final servers before your traffic reaches its destination. They can see what website you’re visiting but don’t know your real IP address.
Why Do People Use Tor?
There are many legitimate reasons people choose to use Tor:
Journalists and activists: Protecting sources and communicating safely in oppressive regimes
Privacy-conscious individuals: Preventing tracking by advertisers and data brokers
Researchers: Accessing information without bias from location-based filtering
Whistleblowers: Securely sharing information about wrongdoing
Everyday users: Simply valuing their right to privacy online
Common Misconceptions About Tor
Let’s clear up some myths. First, using Tor is completely legal in most countries. It’s a privacy tool, just like a VPN or encrypted messaging app. Second, while Tor does provide strong anonymity, it’s not a magic bullet – you still need to follow good security practices. And third, the network isn’t inherently slow; while it’s generally slower than a direct connection due to the routing process, it’s perfectly usable for most activities.
Limitations and Things to Keep in Mind
Tor is powerful, but it’s not perfect. Because your traffic exits through volunteer-run servers, the exit node can theoretically see unencrypted traffic (though not where it came from). That’s why you should still use HTTPS websites when possible. Additionally, Tor doesn’t anonymize everything automatically – you need to be mindful of logging into personal accounts or revealing identifying information.
Getting Started with Tor
The easiest way to use Tor is through the Tor Browser, which is based on Firefox but configured for maximum privacy. It’s available for Windows, Mac, Linux, and Android. The browser handles all the complicated routing for you – just download, install, and browse.
Understanding how Tor works helps you appreciate both its strengths and limitations. It’s a remarkable tool for online privacy, developed and maintained by a community dedicated to protecting internet freedom. Whether you’re a journalist, researcher, or just someone who values privacy, Tor provides a valuable layer of anonymity in an increasingly surveilled digital world.
